The Middle East aerospace and telecommunications industries are the targets of a new cyber espionage campaign aimed at stealing sensitive data about critical assets, infrastructure, and technology while remaining in the dark and evading security solutions.
Cybereason, a cybersecurity firm based in Boston, has dubbed the attacks “Operation Ghostshell,” noting that a previously undocumented and stealthy remote access trojan called ShellClient is being used as the main spy tool of choice. Initial signs of the attacks were observed in July 2021 against a handpicked set of victims, suggesting a highly targeted approach.
Despite being developed since at least 2018, the ShellClient RAT managed to evade antivirus tools and remain undetected, according to researchers Tom Fakterman, Daniel Frank, Chen Erlich, and Assaf Dahan.
The malware was first detected on November 6, 2018, operating as a standalone reverse shell before evolving into a sophisticated backdoor. This indicates that the malware has been continuously developed, with new features added by its authors. In addition, the adversary behind the attacks is also said to have used an unknown executable called “lsa.exe” to perform credential dumping.
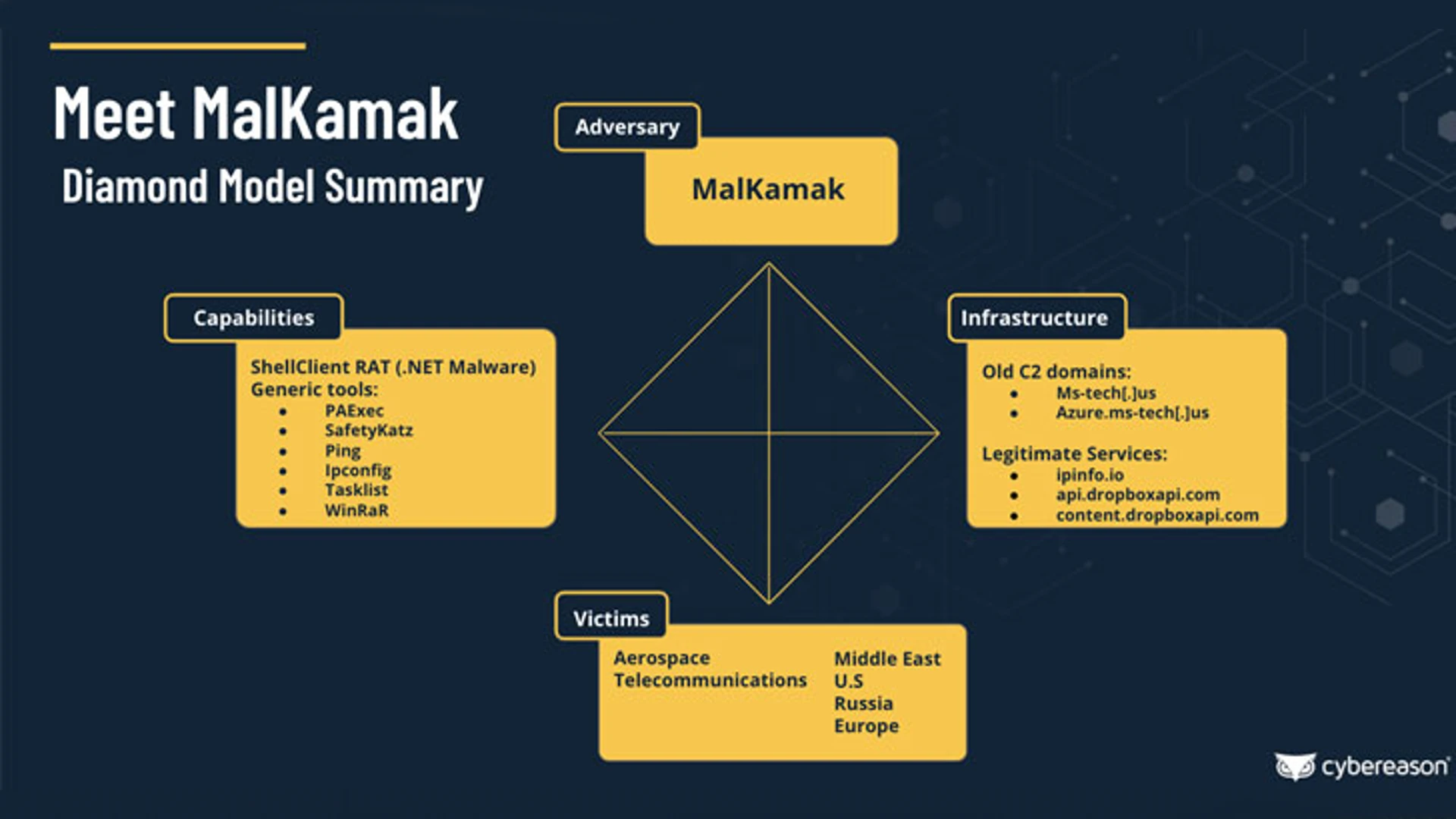
In addition, an investigation into the attribution of the cyber-attacks has uncovered an entirely new Iranian threat actor named MalKamak, which has operated since around the same time period and has thus far eluded detection, with possible connections to other Iranian state-sponsored APT threat actors such as Chafer APT (aka APT39) and Agrius APT, which posed as ransomware operators in order to conceal the origin of data-wiping hacks against Israeli entities.
ShellClient is also capable of performing fingerprinting and registry operations in addition to performing reconnaissance and exfiltrating sensitive data. Another noteworthy aspect is the RAT’s use of cloud storage services such as Dropbox for command-and-control (C2) communications to blend in with legitimate network traffic coming from the compromised systems.
The Dropbox storage contains three folders, each storing information about the infected machines, the instructions to be executed by the ShellClient RAT, and the results of those instructions. Researchers said the victim machine checks the commands folder every two seconds, retrieves files that represent commands, parses the content, then deletes them from the remote folder and enables them for execution.
It was uncovered that another threat actor called IndigoZebra used the Dropbox API to store commands in a victim-specific sub-folder that was retrieved by the malware prior to execution.
Researchers identified an advanced persistent threat called “ChamelGang” behind a string of attacks targeting fuel, energy, and aviation production industries in Russia, the U.S., India, Nepal, Taiwan, and Japan for the purpose of stealing data from compromised networks.